Better safe than sorry
A new ransomware virus attack hit on Tuesday 27th June with its epicentre in Ukraine and quickly spread around the world. This was the largest worldwide attack since the ‘WannaCry’ virus last month.
A Bitcoin payment, equivalent to $300, was demanded to recover encrypted data and it’s believed that this ransom was extorted from only a few of those infected until the payment system was stopped. This has left millions of data files lost forever. The total loss of money and data may never be known but this type of attack is becoming increasingly popular. Clearly ransomware is proving very lucrative for the criminals behind it and the potential economic damage caused by data loss makes state sponsored ransomware attacks inevitable.
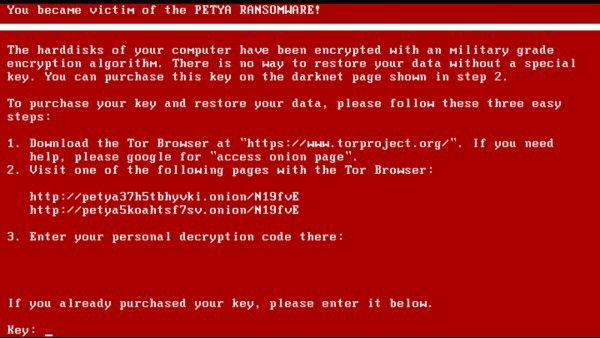
This latest attack is part of the ‘Petya’ family of encrypting ransomware. Petya ransomware updates the Windows Master Boot Record (MBR) boot code with its payload and, while encrypting the NTFS file system at Windows boot time, presents a ransom message on the PC that’s now failing to start.
While the ransomware was encrypting data, Tuesday’s attack showed a fake but credible Windows check disk screen before displaying the ransom demand.
If you’re an individual PC user then don’t be lulled into thinking that these attacks won’t affect you. Even though ransomware attacks tend to be focused on large organizations and businesses, the contagion quickly spreads to vulnerable systems throughout the world.
Prevention is better than cure
So, what can we do to reduce the risk of attack and protect our data if the worst should happen?
Keep Windows up to date with the latest patches
The latest attack exploited a vulnerability in the Windows Server Message Block (SMB) protocol that had been previously patched on every version of Windows, including XP. If your Windows installation was patched up to date then the virus couldn’t spread to you via another networked PC.
Upgrade your PC
This might sound like overkill, but the Petya attack injected its payload into the legacy Master Boot Record (MBR) boot code. Modern PC’s don’t use the MBR to start Windows, and since the introduction of Windows 8, just about every PC uses Microsoft ‘Secure Boot’ which checks the digital signature of the boot code at startup. Modified boot code simply won’t run!
Backup your data
This is crucial. The best way to protect data and recover from a ransomware attack is to have regular backups. You can use Macrium Reflect to create reliable images and file backups of your entire PC and valuable files.
How can I be sure that my backups aren’t vulnerable to attack?
- Backup disk rotation. You can use the ‘Alternative locations’ functionality in Macrium Reflect to regularly rotate (swap) backup drives. For example, using two backup drives, A and B, you can change A for B on a Monday and leave A disconnected from the PC. Repeat the rotation each Monday. Should the worst happen and your backup disk dies or is encrypted by ransomware then you know you have a recent clean backup that’s always available.
- Archive to a remote location. An infected PC won’t be able to harm files on remote storage. This includes the cloud or any location that’s only accessible using secure ftp or http. You can use scripts in Macrium Reflect to automate this or you can copy files using the tools provided by your cloud storage provider.
Open your emails with caution
This is the simplest and most effective preventative measure you can take. If you don’t recognize the email sender or if the attachment or link is unexpected then do not follow or open it. It may be tempting to see what that invoice says and how much you’re being charged by that company you’ve never heard of but don’t open it. Seriously don’t!
Antivirus software
Unfortunately, antivirus software products were initially ineffective for both recent ransomware attacks, though most, if not all, were patched quickly after the initial outbreak. Windows 10 comes with Windows Defender installed for free and Microsoft has done an excellent job of providing a low resource and effective AV solution. Make sure it’s turned on and up to date.
Coming soon — Macrium Image Guardian
To protect Macrium backup files against ransomware attacks our experienced team of developers have developed a new product called Macrium Image Guardian. MIG will be available in the next two weeks and will prevent unauthorized modifying of Macrium backup files on local and USB volumes. Should the worst happen, you can be assured that your latest backups are recoverable. Unlike antivirus software products, MIG is focused on the single task of protecting Macrium files, it has a small footprint and will not impact on the performance of your PC.
This is an essential and exciting addition to the Macrium data protection story! Keep an eye on Macrium and don’t miss our launch announcement and webinar.
You can have a closer look at our data protection solutions and test suitability by downloading our 30 day Trial. If you have any questions don’t hesitate to contact us. Our technicians are always ready to answer any queries you may have.
Techie Tuesday: Windows Explorer shell integration
Organisations should be better prepared for data disasters



