Why is healthcare a target for ransomware?

Ransomware is a rapidly increasing threat to multiple industries. However, according to Beazley, the healthcare industry has been one of the leading sectors affected. For example, there was a 133% increase during the first six months of 2017 alone. But, the sector has a long history of being targeted by cyber criminals.
The first known attack occurred in 1989 and targeted the healthcare industry. As time has progressed, ransomware attacks have become increasingly more sophisticated and continually focused on the weaknesses of the aging IT infrastructure at healthcare institutions.
These attacks not only run the risk of compromising confidential patient data but both the health service capacity and people’s safety too. An Infoblox’s diagnosis revealed that:
- 26 percent of UK and US respondents revealed their organization would pay a ransom.
- 85 percent of those surveyed in the UK said there was a plan in place for this situation.
- 68 percent of US respondents said the same.
When observing these numbers, it is clear that the healthcare industry desperately needs to modernize and update IT services to protect itself from inevitable attack. 60% of institutions now have anti-virus software as their top cybersecurity investment to remove vulnerabilities highlighted by last year’s devastating WannaCry ransomware attack.
Why is healthcare a target?
1. Outdated medical systems that are not adequate for the ever-evolving threats make the industry an easy target. It’s no secret that healthcare is heavily reliant on traditional solutions that are no longer able to protect against new and more sophisticated forms of ransomware.
A recent article from Security Intelligence stated that hospitals invest as little as one-tenth the amount spent by other industries on data security. These known vulnerabilities make the industry an easy target.
2. In Healthcare employees work with extremely sensitive data, and its loss can create a huge risk to patient safety. The entire healthcare service can be forced to stop if they can’t access health records and its patients that will pay the consequences.
Cybercriminals attack these institutions knowing that they would have no other option but to pay the ransom if they do not have the luxury of a backup or disaster recovery plan in place.
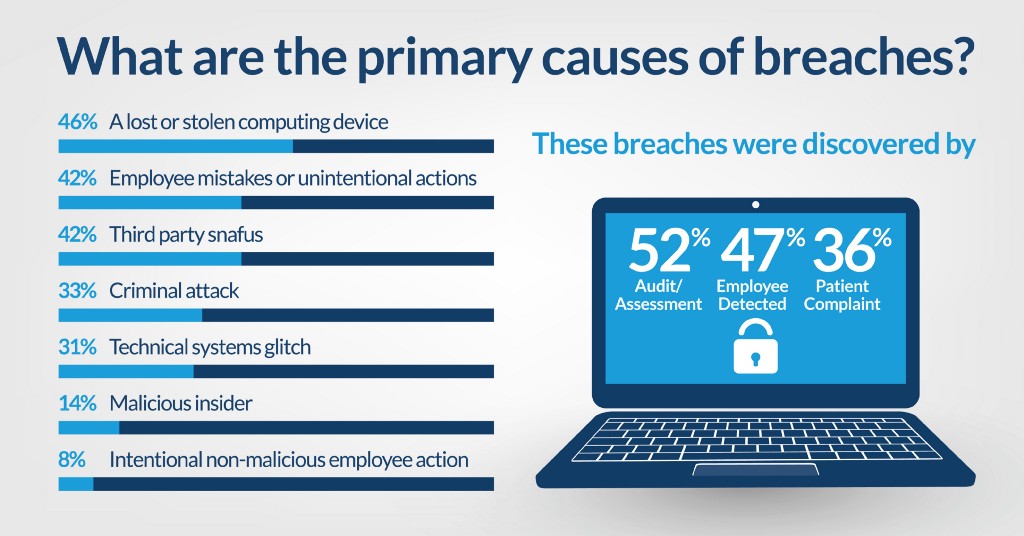
3. Healthcare professionals are humans and as well make mistakes. Falling for phishing scams, picking up a USB flash drive in a carpark or not updating their password on a regular basis can all be the entry point for malware.
Paying the ransom might mitigate the pain but will not be the cure.
Health institutions will be under enormous pressure to deal with a ransomware attack. Being unable to access to patient files and hospital systems can endanger the care of the patient, putting them at risk or in harm’s way. Nevertheless, paying the ransom seldom makes the problem disappear or bring the data back. It won’t protect you from future attacks by the same attacker either. A proactive approach to prevention actions is your greatest defence to reduce the risk of falling to victim to the same attack again.
1. Keep updated: Maintaining Windows involves installing regular updates and patches. Attacks generally exploit vulnerabilities in the systems that are not updated or on the newest version of the software. It important to remember that it was an unpatched Windows 7 and Windows Server 2008 (or earlier OS) systems that opened the door for WannaCry.
Remember to update the version of your backup software solution, as they offer improvements that better protect your backup files when disaster strikes. Our latest release Macrium Reflect 7.1, offers improvements to viBoot and numerous enhancements. The Macrium Image Guardian (MIG) is a feature that protects your backup files against ransomware by preventing unauthorised modifying of Macrium backup files on local and USB volumes.
2. Educate staff. User education is key to winning the fight against ransomware. Remember that by simply opening an infected email the hacker can have access to all your data. Making your employees aware of the security threats can save you from spending millions paying the ransom.
3. Test! Use backups to test scenarios, anticipate disasters and make improvements to your systems. You can do so with our updated viBoot feature, which enables you, to instantly create, start and manage Microsoft Hyper-V virtual machines using one or more Macrium Reflect image files as the basis of the virtual machine storage sub-system.
4. Backup your data: The best way to protect data and recover from a ransomware attack is to have regular backups. You can use Macrium Reflect to create reliable images and file backups of your entire PC and valuable files.
At Macrium we believe that data should be the last of your worries. That’s why we’ve created an exclusive discount for the health sector for you to care about what really matters. You can also have a closer look at our data protection solutions and test its suitability by downloading our 30-Day Trial.
About Macrium Software
Macrium Software provides comprehensive backup and DR solutions for home or businesses which are used worldwide to protect valuable data and operating systems. Using advanced disk imaging technology Macrium solutions provide fast reliable and easily recoverable images. With many millions of users worldwide, Macrium is a trusted and reliable solution for all data protection needs.
Do you want to find out more about our discount or products?
Contact one of our resellers here to get a quote or email us at sales@macrium.com
Sources
http://fortune.com/2017/05/15/ransomware-attack-healthcare/
http://www.healthcareitnews.com/news/ransomware-accounted-72-healthcare-malware-attacks-2016
https://quorum.com/blog/blog/ransomware-in-the-healthcare-sector
http://www.itsecurityguru.org/2017/08/04/mitigating-ransomware-healthcare-sector/
https://www.infosecurity-magazine.com/opinions/treating-ransomware-in-the/
https://blog.shi.com/solutions/ransomware-antidote-health-care/
https://securityintelligence.com/health-care-and-ransomware-a-marriage-made-in-hades/


